The Next-Generation Exposure Management Platform for IoMT, IoT, IT, and OT
Identify, Prioritize, and Mitigate risk across your cyber assets.
Why Asimily?
COMPLETE DEVICE VISIBILITY DONE SAFELY AND TAILORED TO YOUR ENVIRONMENT
Get an accurate inventory of IT, IoT, OT, and IoMT devices, their applications, and their behavior. Safely inventory your network using passive, protocol-based, API-based, or integration-based methods to generate a normalized source of data.
Find Out HowIDENTIFY AND PRIORITIZE THE RISKIEST OF VULNERABLE DEVICES
With a detailed, MITRE ATT&CK-based analysis of each vulnerability from Asimily Labs, learn your true risk for IoT, IoMT, and OT Devices – not just what the vulnerability report says. Use our Risk Simulator to see risk ROI before completing any given action, saving time.
Find Out HowNETWORK SEGMENTATION ORCHESTRATION
Our unique Smart Policy Management feature enables intelligent orchestration and creation of network segmentation policies, ensuring critical cyber assets remain secure with minimal network impact. Users can also preview policy effects before active deployment through the Policy Simulation feature.
Find Out HowMITIGATE RISK AND RESPOND TO THREATS FASTER
In addition to a comprehensive approach to risk reduction through Targeted Attack Prevention, Device Patching, and Segmentation, Asimily also provides anomaly detection and incident response support to strengthen your security posture by identifying potential threats, enforcing policies, and packet capture capabilities.
Find Out HowCompliance-Ready with Ease
With detailed reporting, record-keeping, device timelines, password management, and Configuration Control, you have what you need to adhere to compliance and regulatory requirements such as Zero Trust, HIPAA, FDA, NIST CSF 2.0, NERC CIP, and more.
Find Out HowReduce Risk Faster
Asimily analyzes each vulnerability using patented AI/ML and Asimily Labs experts. No stopping at basic categorization. Find out the real risk faced, and how to quickly eliminate it. Asimily customers typically remove more than 10,000 high-risk vulnerabilities in their first 3 months.
Find Out How
Don’t Stare at Dashboards – Take Recommended Action Now
Offers every technique possible to reduce risk now – microsegmentation, targeted attack prevention (180+ types), and patching – a device at a time or automatically.
Find Out How
Secure Your Devices with IoT Patching
Install new, safe firmware for IoT devices in just a few clicks (or none). Speed up IoT patching and password management of devices with a click of a button.
Find Out How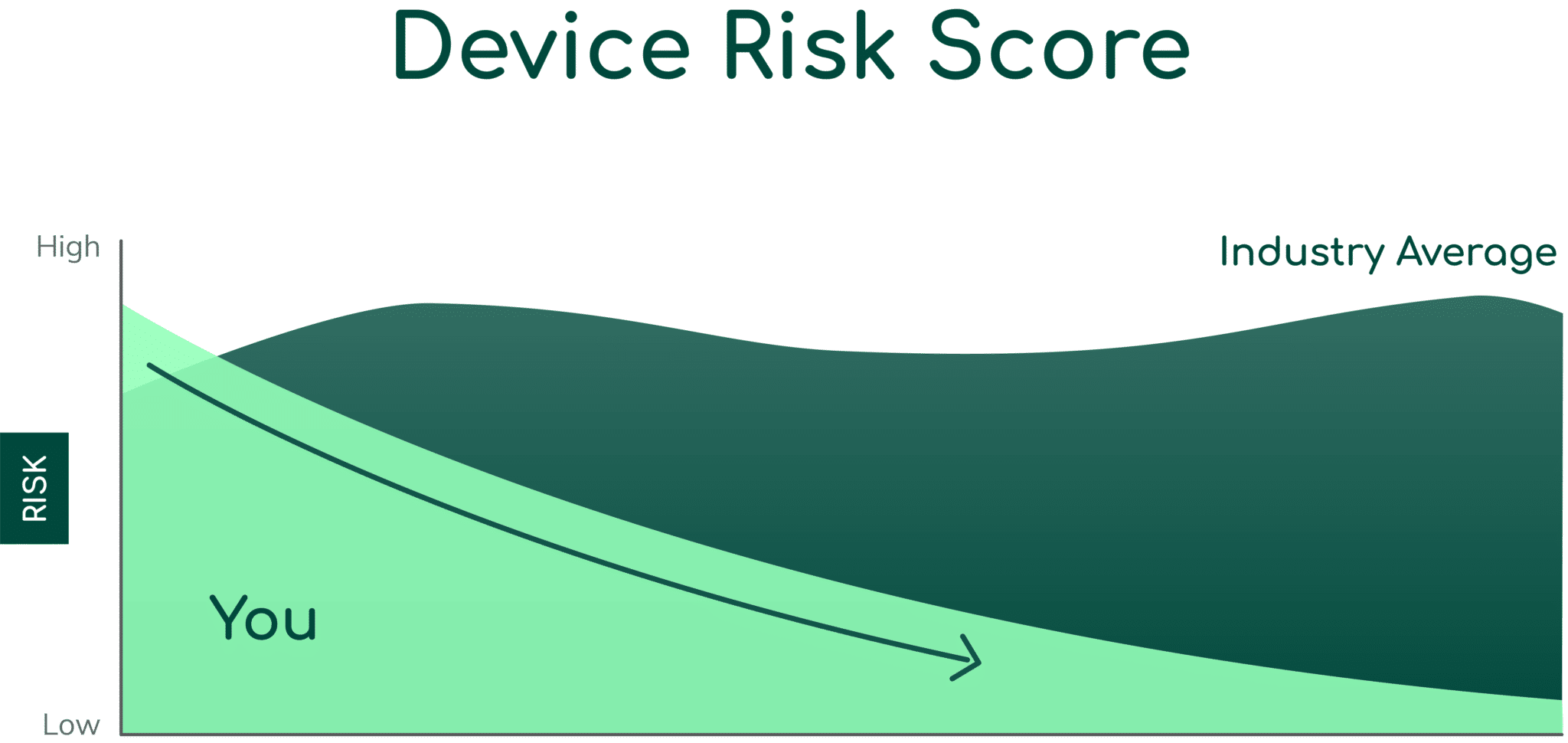
Read the Latest from Asimily
Secure Every IoT Device.
Automatically.
Cyber threats move fast — so should you. Asimily gives instant inventory and smart, prioritized risk mitigation insights for every IoT, OT, and IoMT device — so you can take action before threats strike.